“ACC needs to establish how Enterprise Logging Ingest & Cyber Situational Awareness Refinery (ELICSAR) will enable data driven decisions to maximize capability value to defensive cyber operation (DCO) operators, and the broader Air Force community.”
– Ms. Linda Halverson, Technical Advisor of Information Warfare Systems Division, HQ Air Combat Command A52K
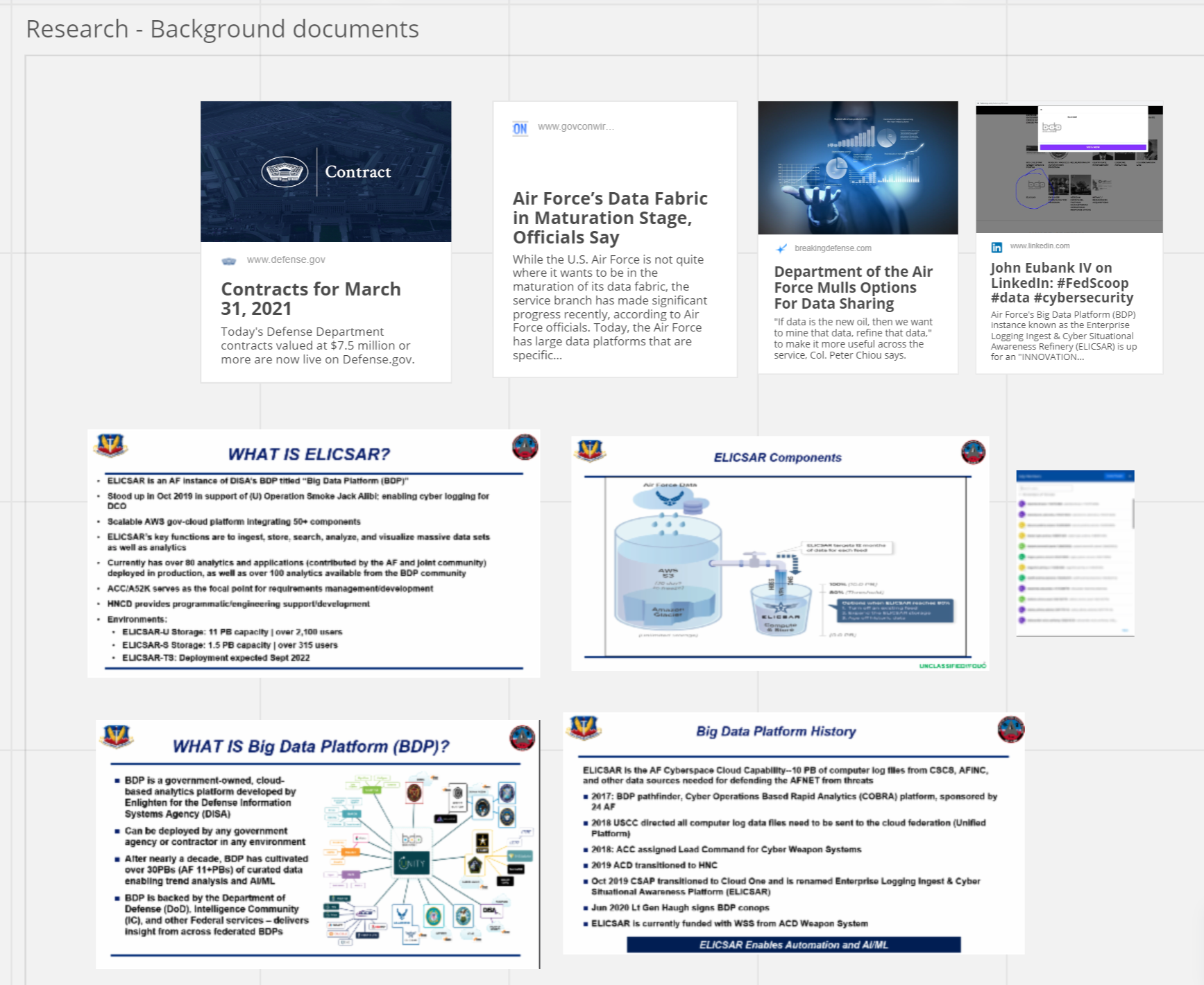
You immediately notice the sense of urgency with Ms. Linda Halverson’s word choice in stating that “ACC needs to…”. This sentence was part of her assessment on the cyber data governance problem within ELICSAR. The A52K team understands the importance of cyber operations across the Diplomatic, Information, Military and Economic (DIME) arena and acknowledges that resiliency in the defense ecosystem will be paramount.
Ms. Linda Halverson described ELICSAR as the Defense Cyber Operations (DCO) big data platform (BDP) and how It serves as a critical core component to defend the Air Force Information Network (AFIN). She described that although ELICSAR has successfully ingested a broad array of diverse structured data sources, it continues to lack in computing and storage resources. What ELICSAR needs: a sustainable cyber data retention strategy.
She approached the AF CyberWorx team, and together they refined the need into a problem statement that could be further researched:
The pace of cyber data use within ELICSAR will continue to accelerate; therefore, it is essential to understand the current cyber data retention characteristics for hot, warm, and cold storage for the 16th Air Force.
ELICSAR is arbitrarily moving data into cold storage to maintain an 80% storage capacity threshold to mitigate slow queries. But we don’t want slow for the DCO BDP, and arbitrarily is not sustainable for that much data.
How can we determine what cyber data feeds are the most essential for DCO missions? How can ACC define a cyber data governance strategy?
With the problem defined, the AF CyberWorx team dove in with user research:
- 15 stakeholder/user interviews, with each user identifying different needs
- Analyzing BDPs efforts across the services: Navy, Marine Corps, and Army
- Discovering the tasks completed within ELICSAR across the 16th Air Force
- Identifying pain points with cyber data and the usage of the suite of applications found within ELICSAR
- Exploring future opportunities to provide recommendations on next steps to optimize the use of cyber data
In this user research, AF CyberWorx’s interview questions exhibited user-centric problem-solving. Here’s a sampling:
Tell us about the last time you used ELICSAR
How have you used ELICSAR to solve a DCO problem?
What are the hurdles to success with ELICSAR?
How long have you used cyber data stored within ELICSAR ?
How would you prioritize the cyber data feeds in ELICSAR?
Research led to several discoveries: ELICSAR is currently being used as a reactionary tool. Some applications are difficult to navigate, and many users are not aware of all that ELICSAR can provide for their unit. Several applications are being developed under the Joint Cyber Command and Control (JCC2) program management office which the Air Force is managing on behalf of Cyber Command and the joint cyber force. Usage frequency ranges from daily to monthly, and retention of cyber data in hot storage ranges from 7 days to 90 days.
A key method throughout the user research was using Human-Centered Design to understand:
- Pain points experienced by ELICSAR users from novice to senior-level
- Anchors holding ACC down from making progress with a cyber data retention strategy
- Collective requirements that need definition for Cyber Command’s ideal state for BDPs
Three recommendations emerged after the research, which turned into three calls to action:
- 1
Propose cyber data retention of 30 days with 30 working-day period.
- 2
Model the behavior to incite desired behavior by ELICSAR users.
- 3
Define quantitative insights to help prioritize cyber data feeds for the 16th Air Force.
Propose 30-day cyber data retention in hot storage
Based on user feedback, moving forward with a shorter hot storage timeline would expedite the use cases for cyber data that is needed for longer periods of time.
Model the behavior to incite desired behavior
There are regular ELICSAR Team meeting engagements, but few are aware of them. What ELICSAR can do for DCO units needs to be communicated, and standardized templates should be shared.
Define quantitative insights to prioritize 16th AF cyber data feeds
To make sense of ELICSAR quantitative usage of cyber data feeds is important to guide how the 16th Air Force will work to prioritize which cyber data feeds are impacting DCO mission sets. This will then help determine how long cyber data feeds should remain available in hot versus cold storage.
The next step: gain stakeholder buy-in for a design sprint that will combine the insights and expertise of military, government, and industry participants.
ELICSAR has a properly defined problem: it lacks cyber data governance. However, for ACC A52K to proactively move forward with confidence in shaping the future of ELICSAR, they must ensure the users, cyber operators, are at the forefront in making the decisions for a future cyber data retention strategy.
Did you find this informative? Learn more about our other projects!